THE tremendous capacity of today’s optical networks is capable of supporting the growing traffic demand of the Internet, data centers and cloud computing systems. Because optical data channels can be easily compromised via fiber tapping, there are growing concerns over the security and privacy of optical networks. To address these concerns, optical signal processing has been used to enhance security and privacy in the physical (optical) layer.
Secure key distribution based on localized and asymmetric fiber interferometers
Secret key generation and distribution are indispensable for secure and private communications. Public key cryptography is now the most commonly adopted key distribution method. Its security depends on the computational hardness, which may become vulnerable with the rapid development of computing technologies, e.g., quantum computing.
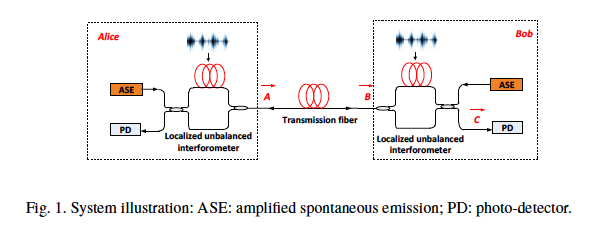
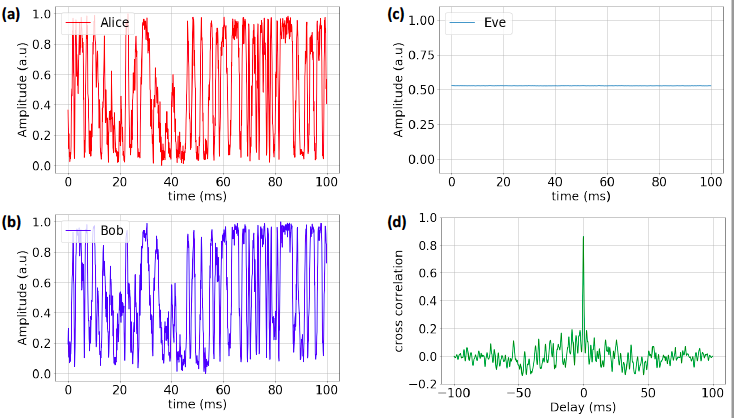
We developed a method for generating and sharing a secret key over an existing optical fiber communication infrastructure. Mach-Zehnder interferometers (MZIs) are adopted for key generation by transferring the environmental instability to random optical signals. A novel combination of ultra-wideband optical noise and an asymmetric MZI structure hides the key signal in the wideband noise, thus enabling the secret key to be securely transmitted over public channels. This key generation and distribution system provides reliable performances: a one-time pad key generated at the rate of 6.3 kbit/s with a bit error of 2%, and transmitted over a distance over a 10 km optical fiber. Our proposed system is a cost effective and reliable solution for the key establishment and compatible with the existing optical fiber communication infrastructure.
Photonic Layer Security
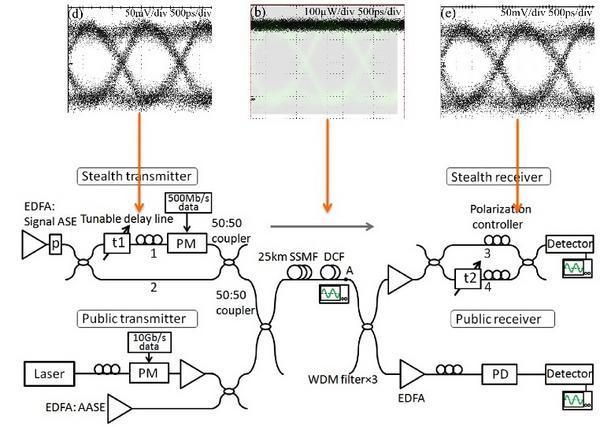
Optical steganography allows information to be sent in secret. In the example above, a signal is encoded within noise itself, preventing eavesdroppers from knowing whether the message was even transmitted. Nonetheless, the signal can re-emerge when the intended receiver applies the correct 'physical key.'
Processing delays make the provision of data security costly for high speed transactions. Whereas information can be communicated over long distances through optical fibers at the speed of light, data encryption is bottlenecked by electronics. Traditional digital signal processing encryption can be a deal-breaker: it often takes a computer more time to encrypt a packet of data than for that packet to travel from New York to Chicago. The choice then becomes a trade-off: stay secure, or postpone the arrival of information. We are embarking on a new research program in which data is encrypted at the speed of light---not with conventional computers, but with ultrafast optical processing technology that provide zero latency connections.
Our approach is based on several advanced technologies developed at Princeton. The first is the implementation of digital encryption with all-optical logic gates. One example of this is the patented TOAD exclusive-OR gate, in which tiny lasers play the role of transistors. The second is a system based on optical steganography that conceals optical data in plain sight, making it physically impossible for eavesdroppers to detect incoming signals without a 'physical key.' Some of our recent breakthroughs in optical steganography include pushing signals below the noise floor and coding information in the noise itself, preventing eavesdroppers from even knowing that messages are being sent. Technology development in this sector could potentially lead to ultrafast, secure data transmission, useful in applications ranging from high-security communications to high frequency trading.
Book Chapters
Journal Papers
B. Wu, A. N. Tait, M. P. Chang, P. R. Prucnal, “WDM optical steganography based on amplified spontaneous emission noise,” Optics Letters, vol. 39, no. 20, 5925–5928, 2014.
B. Wu, B. J. Shastri, and P. R. Prucnal, “System performance measurement and analysis of optical steganography based on amplifier noise,” IEEE Photonics Technology Letters, vol. 26, no. 19, pp. 1920–1923, Oct. 2014.
B. Wu, M. P. Chang, B. J. Shastri, Z. Wang, and P. R. Prucnal, “Analog noise protected optical encryption with two-dimensional key space,” Optics Express, vol. 22, no. 12, pp. 14568–14574, Jun. 2014
K. Kravtsov, Z. Wang, W. Trappe, and P. R. Prucnal, “Physical layer secret key generation for fiber-optical networks,” Optics Express, vol. 21, no. 20, pp. 23756-23771, Oct. 2013.
B. Wu, Z. Wang, Y. Tian, M. P. Fok, B. J. Shastri, D. R. Kanoff, and P. R. Prucnal, “Optical steganography based on amplified spontaneous emission noise,” Optics Express, vol. 21, no. 2, pp. 2065–2071, Jan. 2013.
Z. Wang, M. P. Fok, and P. R. Prucnal, “Physical encoding in optical layer security,” Journal of Cyber Security and Mobility, vol. 1, no. 1, pp. 83–100, Jan. 2012.
Conference Papers
J. Chang, N. Cvijetic, T. Wang, and P.R. Prucnal, “Adaptive photonic beamforming for physical layer security of mobile signals in optical fronthaul networks,” submitted to Frontiers in Optics (FIO), Tucson, AZ, USA, Oct. 2014, paper FTh1B.
B. Wu, M. P. Chang, Z. Wang, B. J. Shastri, and P. R. Prucnal, “Optical encryption based on cancellation of analog noise,” in Proc. Conference on Lasers and Electro-Optics (CLEO), San Jose, CA, USA, Jun. 2014, paper AW3P.5.
B. Wu, Z. Wang, B. J. Shastri, Y. Tian, and P. R. Prucnal, “Phase mask encrypted optical steganography based on amplified spontaneous emission noise,” in Proc. IEEE Photonics Conference (IPC), Seattle, WA, USA, Sep. 2013, paper MG3.3, pp. 137–138.
B. Wu, Z. Wang, B. J. Shastri, Y. Tian, and P. R. Prucnal, “Two dimensional encrypted optical steganography based on amplified spontaneous emission noise,” in Proc. Conference on Lasers and Electro-Optics (CLEO), San Jose, CA, USA, Jun. 2013, paper AF1H.5.
Group Members:
- Paul Prucnal, Professor of Electrical Engineering
- Ben Wu, Graduate Student
